Overview
As organizations modernize their identity and access strategies, many find themselves constrained by legacy infrastructure decisions made years (or even decades) prior. One EMBER client, a security-conscious financial services firm, set out on an ambitious initiative: fully retiring on-premises Active Directory (AD) and migrating to a cloud-only Microsoft Entra ID identity model.
What initially appeared to be a straightforward infrastructure cleanup quickly revealed itself to be a deeply interconnected transformation touching identity, networking, security tooling, applications, and end-user workflows. EMBER partnered closely with the client to methodically plan, validate, and ultimately execute a successful Active Directory retirement which assists in laying the foundation for a more resilient, cloud-native future.
The Challenge
Over time, the client’s domain controllers had evolved beyond their original purpose and effectively became a central dependency layer within the environment. Numerous systems relied on Active Directory directly or indirectly. This included application authentication, name resolution, endpoint management, and security tooling.
The assumption that Active Directory would always exist led to intermingled configurations and implicit dependencies that were not immediately visible. Decommissioning domain controllers without a full understanding of these relationships posed a significant operational risk, particularly given the client’s sensitivity to downtime and service disruption.
The challenge was not simply replacing directory services but systematically identifying and removing every reliance on Active Directory while maintaining business continuity.
The Approach
EMBER began the engagement with a comprehensive dependency assessment. This involved auditing all known and potential integrations with Active Directory, including software platforms, internally developed applications, security services, group policies, and domain-joined assets. Particular attention was given to services that relied on legacy authentication protocols or domain-based DNS resolution.
Once the dependency landscape was documented, EMBER worked with the client to prioritize remediation efforts. Dependencies were ranked based on business criticality and complexity of resolution. This allowed the project to progress in a controlled manner, addressing the highest-risk items first while steadily reducing the overall dependency footprint.
Execution required coordination across multiple teams. EMBER worked closely with developers to refactor or reconfigure applications, with infrastructure teams to migrate systems and remove legacy configurations, and with end users to transition devices to cloud-native identity. Redundant domain controllers were gradually decommissioned as dependencies were resolved and validated.
Validation and Discovery
After several months of remediation and testing, the environment reached a point where all identified Active Directory dependencies had been addressed. A planned test was scheduled to take the remaining domain controllers offline.
During this test, several critical application connections failed. EMBER quickly restored services by bringing the domain controllers back online and initiated a root cause analysis. The issue was identified quickly and resolved before business operations were impacted.
The root cause was traced to DNS resolution behavior within the client’s Zscaler ZPA App Connectors. While application authentication had been fully decoupled from Active Directory, the connectors were still resolving internal DNS queries through the legacy domain controllers. This represented an implicit infrastructure dependency rather than an identity dependency and was not surfaced during earlier phases of remediation.
The Solution
Following the validation exercise, EMBER conducted a full review of DNS architecture within the ZPA App Connector environment. Rather than modifying production connectors in place, EMBER designed a parallel deployment strategy.
New ZPA App Connectors were deployed with DNS resolution aligned to the client’s cloud-native architecture. This approach created a future-state environment that could be tested independently while the existing configuration continued to support the broader user base. Users were migrated incrementally, allowing for validation of application access and DNS behavior under real-world conditions.
Once testing was complete and users had been successfully transitioned, the legacy connector configuration was retired.
The Outcome
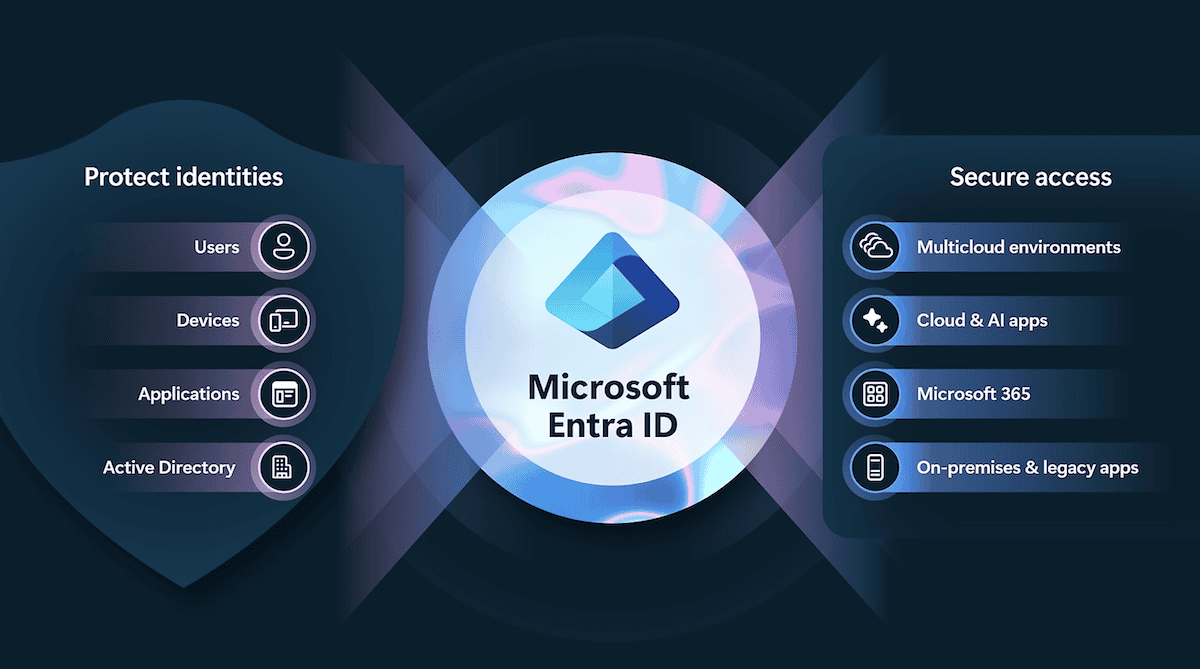
With all identity and infrastructure dependencies fully removed, EMBER executed the final shutdown of the remaining domain controllers. Active Directory was formally retired, completing the client’s transition to a cloud-only Entra ID model.
The engagement resulted in a simplified identity architecture, reduced infrastructure overhead, and improved alignment with Zero Trust principles. The client eliminated a significant source of technical debt while gaining greater confidence in the resiliency and transparency of their access architecture.
Conclusion
Retiring Active Directory in a mature environment requires more than technical execution. It requires disciplined discovery, structured remediation, and deliberate validation. EMBER’s methodical approach ensured that both explicit and implicit dependencies were addressed, allowing the client to modernize identity services without compromising stability or security.
This engagement demonstrates EMBER’s ability to guide complex infrastructure transformations and deliver cloud-native outcomes for organizations with high operational and security requirements.